Secure Bring-Your-Own-PC Technology
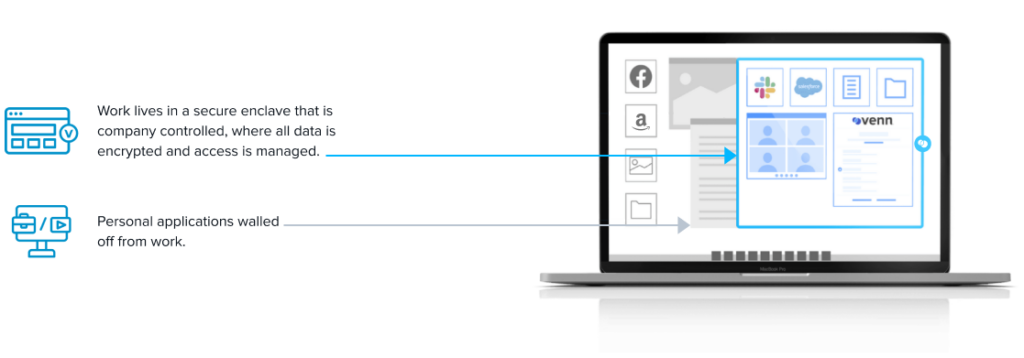
Remote work can now easily be secured on any PC or Mac without VDI. With Venn, work lives in a company-controlled Secure Enclave installed on the user’s PC or Mac, where all data is encrypted and access is managed.

The Secure Workspace for Remote Work
Venn secures remote work on any unmanaged or BYOD computer with a radically simplified and less costly solution than VDI.
Zero Backend Infrastructure
Venn is a new approach to securing remote workers. Instead of deploying virtual desktops or having to buy, manage and lock down every PC, Venn makes Secure BYO-PC cost-effective and simple.
The Secure Enclave
Similar to an MDM solution but for laptops – work lives in a company-controlled Secure Enclave installed on the user’s PC or Mac, where all data is encrypted and access is managed. Work applications run locally within the Secure Enclave – visually indicated by the Blue Border™ – where business activity is isolated and protected from any personal use on the same computer. Company data is now protected without having to control the entire device, and as a result, remote work is secured without the cost, complexity and performance issues of VDI.

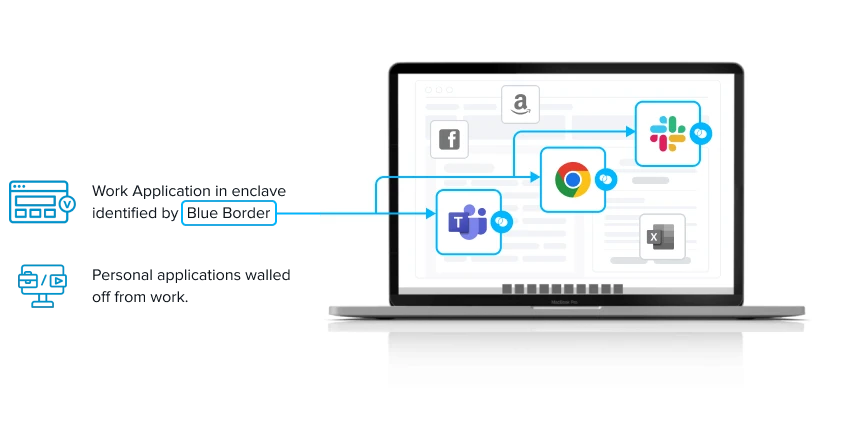
The Blue Border
Venn took a very different approach with the Blue Border. Venn requires zero backend infrastructure. It’s a patented software-based solution that puts a virtual wrapper around work applications running locally on the computer. It’s simple to use, cost-effective and easy to support. It’s secure and complies with regulatory requirements, and companies can onboard and offboard remote workers in minutes.
Virtual Desktop Alternative
Virtual Desktop Infrastructure, which has long been the de facto approach to protecting apps and data on remote and unmanaged computers, is increasingly being recognized as a less-than-ideal choice. VDI is complex, expensive and often frustrates users. It’s redundant for browser-based applications and doesn’t perform well with video applications

Optimal Performance and Experience on any PC or Mac
Unlike VDI, which has latency and performance issues, work applications are launched directly from the computer and run locally, not a remotely-delivered desktop, providing optimal performance and a familiar experience.
Stop shipping laptops!
Get out of the hardware business. Reduce or eliminate the cost and complexity of buying, managing and shipping company-owned PCs and Macs.
Turnkey Compliance
Venn was purpose built to comply with the strictest industry standards, including: PCI, SOC, HIPAA, SEC, FINRA, NAIC and more.
Before Venn, we were not allowing BYO-PC and we were deploying computers for every person. Our struggle was because of all of our security tooling. To meet our benchmarks, we had to buy 1,000 dollar laptops to meet all the requirements and make it so that they could work. If we can get rid of just a portion of our laptops a year, it basically pays for all Venn users.





Previous
Next
How Venn protects applications and data inside the Blue Border™
Venn secures remote work on any unmanaged or BYOD computer with a radically
simplified and less costly solution than VDI.
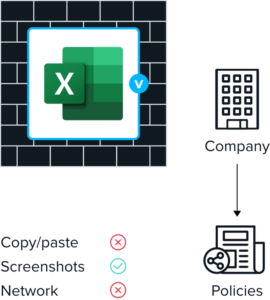
Centralizes administrative control over work data, application and peripheral use
Provides ability to remotely enable, suspend, terminate or wipe at press of a button
Ensures that all network access
is policy–controlled and routed
through encrypted private
company gateway
Device compliance check gate access, enforcing hygiene & compliance policy
Applications Isolation
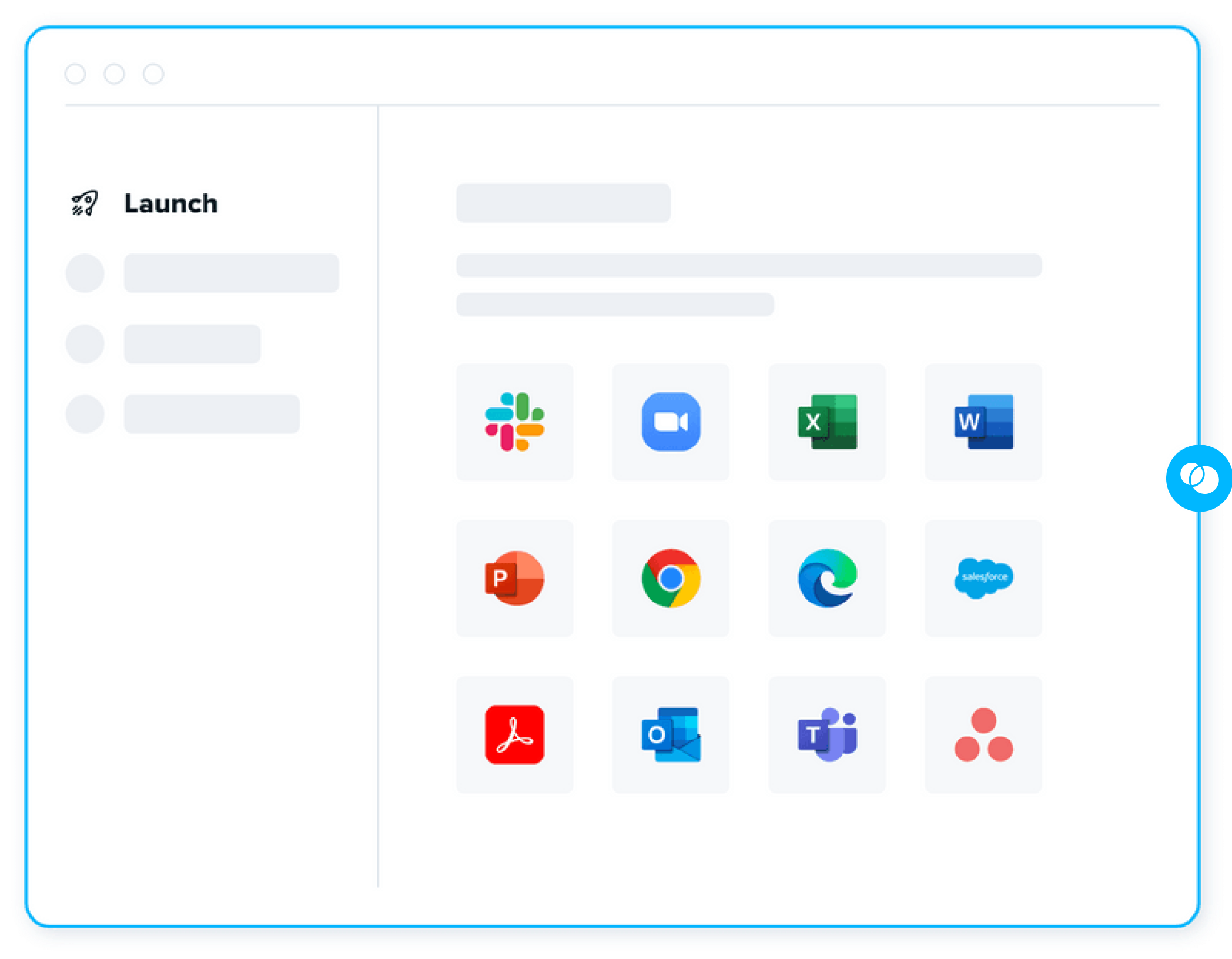
With Venn you can protect all work applications. Chrome, SaaS Apps, Office 365, Edge, Adobe, Safari, Web Conferencing (Zoom, Webex, Teams, etc) and many other apps. Work applications run locally within the enclave – visually indicated by the Blue Border™ – where business activity is isolated and protected from any personal user on the same computer.
How Venn protects applications and data inside the Blue Border™ The Secure Enclave for Work
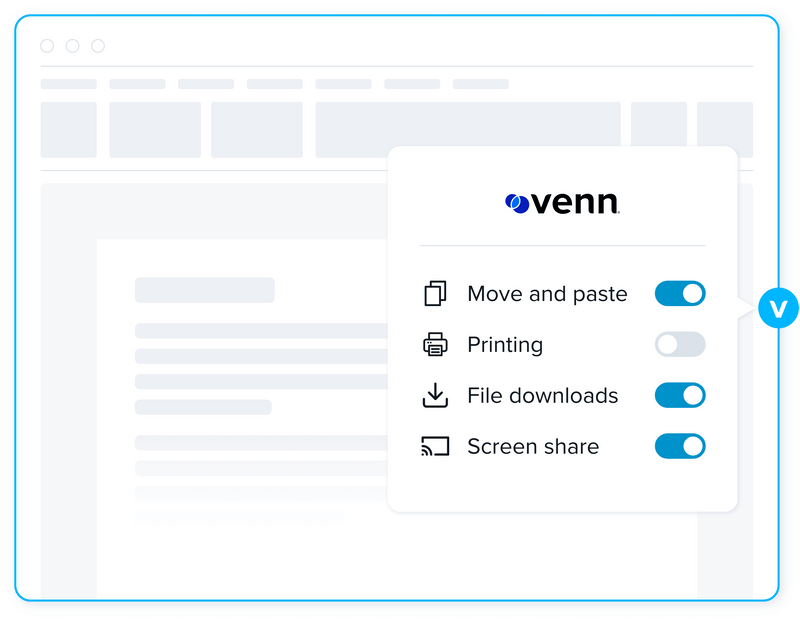
When a user launches an application in ‘work’ context, Venn puts a virtual wrapper around it, visually indicated by the Blue Border around each application window. That work application is then running inside of the Secure Enclave, which acts like a firewall, controlling what can go in or out. Security policies include the ability for customers to restrict moving data, printing, clipboard copy/paste, screen sharing, uploads and more. Security policies can be very granular and can be specifically applied to any individual user or a group of users.
Unlike VDI, work applications are launched directly from the computer and run locally, not a remotely-delivered desktop, providing optimal performance and a familiar experience.

An app gets launched in
Windows/Mac.
Windows/Mac.
Venn detects work app.
Puts virtual wrapper
around it.
Puts virtual wrapper
around it.
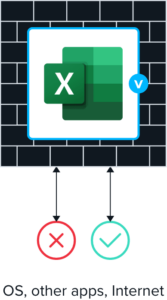
Wrapper acts as firewall.
Controls what goes in and
out.
Controls what goes in and
out.
Policies govern
entitlements.
entitlements.
Fine Tune Security Policies to Fit Your Organization
Venn’s configurable policies control which applications are purposed for work and only applications assigned to a user by an admin are permitted to run in Venn. Once inside the enclave, applications are subject to admin configurable DLP policies that govern functions such as copy/paste, screen sharing, printing, downloads and more.

Data stored in Venn is always encrypted and
inaccessible to any application outside of the
enclave, while data in transit is routed through a
built–in encrypted private company gateway or a
VPN/network security system already employed by
your organization. Access to Venn can be enabled,
suspended, terminated or data remotely wiped, with
a click of a button.
inaccessible to any application outside of the
enclave, while data in transit is routed through a
built–in encrypted private company gateway or a
VPN/network security system already employed by
your organization. Access to Venn can be enabled,
suspended, terminated or data remotely wiped, with
a click of a button.
Purpose built with the
highest standards
Venn was built to comply with the strictest
cybersecurity standards including:
- SOC 2 Type II
- HIPAA
- SEC
- FINRA
- NAIC
- NYS DFS
- Mass 201 CMR 17.00

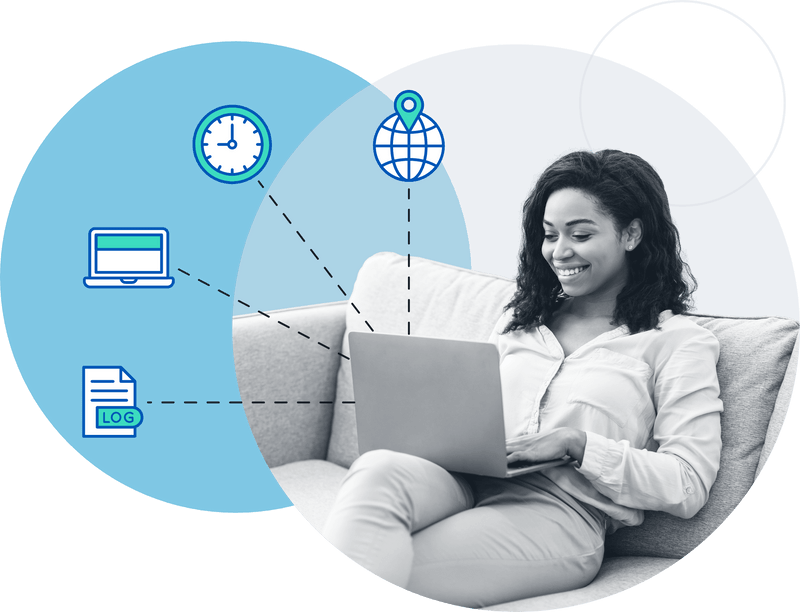
Simplified Administration
With Venn, companies can onboard and offboard remote workers in minutes. And with centralized administration it is easy to understand and easier to use while providing complete visibility and control. Insights into real–time user activity and device inventory ensure you always know where, when and from what device a user accessed an application or quarterly financial data, together with extensive compliance–ready logging.
Venn’s DLP policy admin delivers complete control over how those applications and data are used including copy/paste, screen sharing, and additional controls. Comprehensive visibility and control without the learning curve.

Seamless Integrations
Venn was built on the premise that your organization wants best of breed solutions. You’ve done your research, and invested significant time, energy and resources implementing them. That’s why Venn was built with an integration–first mindset and seamlessly connects to your existing tech stack.
Manage user identities with Okta or Azure and leverage MFA solutions such as DUO or ESET. Restrict application connections to the Secure Enclave, locking down the network traffic to your VPN or SASE solutions like ZScaler, CATO, or Umbrella. Connect to OneDrive or Box and gain access to critical documents locally and on demand. Venn enables you to keep the best of what you have, while keeping work inside the Blue Border.
Secure BYO-PC is the Future
Companies and employees equally benefit. Secure BYO-PC technology is not just about reducing hardware costs. As with mobile phones and MDM, narrowing company control to only within the Secure Enclave fundamentally simplifies the scope and cost of securely onboarding remote workers. Security and compliance-driven companies gain protection for what counts and employees enjoy more freedom, flexibility and privacy. Freedom without compromise.
That’s a vision worth investing in and striving for.

Product Videos
Watch our product videos to learn more. Our series of short videos walks through how you can onboard employees in minutes, prevent printing or copy paste, control access to sensitive access, and more.
Resources and Insights

The Future is Local - Embracing a Modern Alternative to Legacy VDI
The reality of modern work has eroded the promise and potential of VDI. Learn how the new technology can empower MSPs and IT leaders to solve for today's IT challenges.
9 Questions to Test Your Readiness for a Hybrid Workforce
Many well

A Brief History of Virtual Desktops and What's to Come
When virtual desktops first burst onto the scene, it was a revolutionary time for the tech industry. Fast forward to the 2020s. The future is about providing users with a local experience.