Securing Contractors and Offshore Workers
Secure remote third-party contractors and offshore workers on any user-owned or unmanaged BYOD PC or Mac without the cost and complexity of VDI. Venn helps keep contractors productive and secure.
Secure BYO-PC for Contractors and Offshore Workers
Contractors, offshore workers, freelancers and other third parties – this significant part of the work ecosystem offers businesses a more flexible workforce. The challenge has been onboarding/offboarding them quickly and ensuring sensitive data is protected. Shipping and locking down devices or provisioning virtual desktops to ensure secure access is time consuming and costly. Venn changes all that with Secure BYO-PC.

Flexibility
Secure remote work on any user-owned BYOD or unmanaged PC or Mac computer.
Security
Maintain full control over sensitive company data and meet compliance for HIPAA, PCI and more.
Control
Gain robust administrative control over work apps and data including policies for network access, peripheral use, copy-paste and more.
Deployment
Gain a fast and simple way for IT to securely onboard and offboard workers in minutes.
Venn is the secure workspace for remote work that isolates and protects work from any personal use on the same computer. Gain maximum flexibility for your contractors while keeping sensitive data and applications secure on any user-owned or unmanaged device.
Gartner, Inc. “Hype Cycle for Endpoint Security, 2023” by Franz Hinner, Satarupa Patnaik, Eric Grenier, Nikul Patel and “Hype Cycle for I&O Digital Workplace Transformation, 2023” by Autumn Stanish, Pankil Sheth
Secure BYO-PC
With Venn’s Secure Enclave, you can ensure all company apps and data are isolated and protected from anything else on the same computer.
Keep access for contractors limited to only the information and resources necessary to perform their jobs.

Maximum Flexibility
Allowing third party contractors to use their own device ensures they can onboard more quickly and get to productivity faster. IT teams can save the time, frustration and expense of buying, managing and shipping laptops back and forth.
Turnkey Compliance
When working with contractors, keeping sensitive data safe and secure is a priority Venn provides turnkey compliance for HIPAA, PCI, SEC, SOC 2 and more making it easy to execute on any compliance requirements you need to meet.

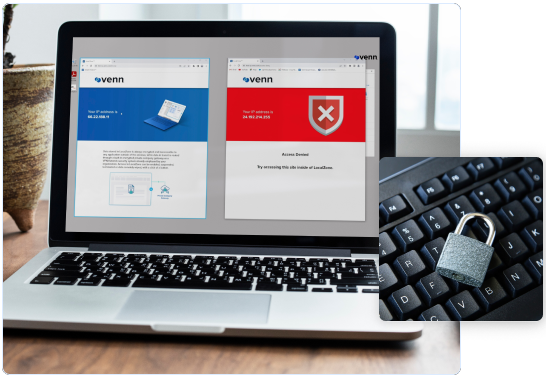
Robust Security Controls
IT administrators can take advantage of flexible security controls to help improve contractor access and productivity while providing user flexibility. Venn enables robust administrative control over work applications and data including policies for network access, peripheral use, copy–paste and more.
Onboard and Offboard with Ease
Onboarding and offboarding contractors and third party workers can be challenging especially during times of seasonality when there can be a large flux of workers to manage. With Venn you can onboard workers in minutes and when they leave, all work data can be instantly and remotely wiped keeping all sensitive data secure.
Save Costs
VDI is a popular choice for securing third party contractor and offshore worker devices. Venn is less costly, less complicated and preferred by users. Users can work on their own devices and IT teams save on the cost of VDI or having to lock down and ship PCs back and forth.
Venn is making MDM for Laptops
With Secure BYO-PC, users work natively using the same applications they normally would. Yet, all company data stays isolated and protected from anything else on the same computer.
- No change in how users work.
- No stress for IT and security leaders.
- It's the best of both worlds.

How to Provide Data Security and Compliance for Remote Contractors
Minimize Risks from Independent Contractors, Offshore Workers, Gig Economy, and other third parties.
In this Whitepaper, you will learn about:
- How non-traditional workers are creating a growing security risk
- The six capabilities you must develop to secure your non-traditional workers
- Why current tools and processes are failing, and how new secure BYO-PC tools help


